Because of the recent security incident involving Instructure, the parent company of the Canvas Learning Management System, users should be extra cautious about phishing emails. Clemson University uses Canvas, so we may be at a higher risk of targeting.
Targeted Phishing emails are highly personalized cyberattacks that use collected, detailed information about a person to craft emails that are potentially more detailed and convincing. These types of targeted phishing campaigns often follow major cybersecurity events.
The Instructure company has reached an agreement with the hackers for the return and destruction of any stolen data, but users should still exercise additional caution with emails.
Some of the ways to avoid falling for a phishing email are:
- Carefully check the sender’s name and email address
- Beware of requests for immediate action
- Look for grammatical and spelling errors
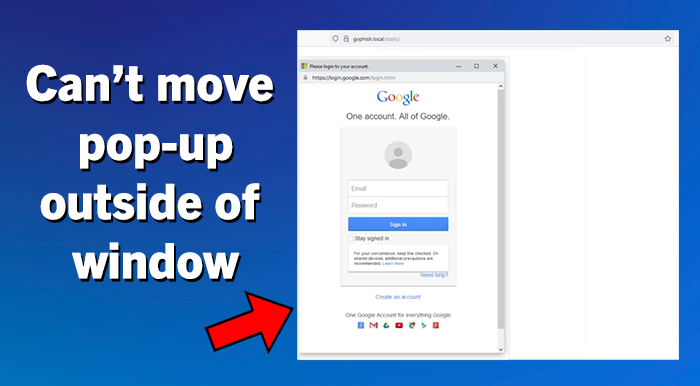
- Be careful of website links in an email
- Avoid opening email attachments
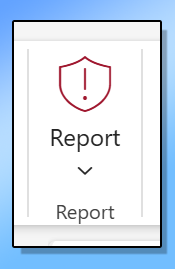
If you do get a suspicious email or even one that you are not sure about, simply submit it to the Clemson Cybersecurity Team for review by using the Report button in Outlook or forwarding it to phishing@clemson.edu. Additional information is available on the Reporting Phishing Emails webpage.